When Anthropic's Mythos Preview dropped, the headlines focused on cyber stocks. Behind the noise, security and engineering teams were asking a harder question: how do we actually prepare? Anthropic published their answer: seven concrete recommendations for defending against AI-accelerated offense. It's worth reading carefully.
What struck us reading it: every recommendation points toward the same structural gap. Legacy application security was built for a world where both sides moved at human speed. Scanners, ticket queues, and periodic audits worked when the window between disclosure and exploitation was measured in weeks. That window is now measured in hours, and sometimes even minutes.
AppSec tools aren't in the solution space Anthropic is describing, they were built for a different threat era. Even most runtime players address only one or two of the three capabilities Anthropic points to: function-level reachability, internet-level exposure, and continuous inventory as the basis for threat modeling. Miggo was built on all three.
Here's how Anthropic's seven recommendations map to what Miggo does.
The Comparison at a Glance
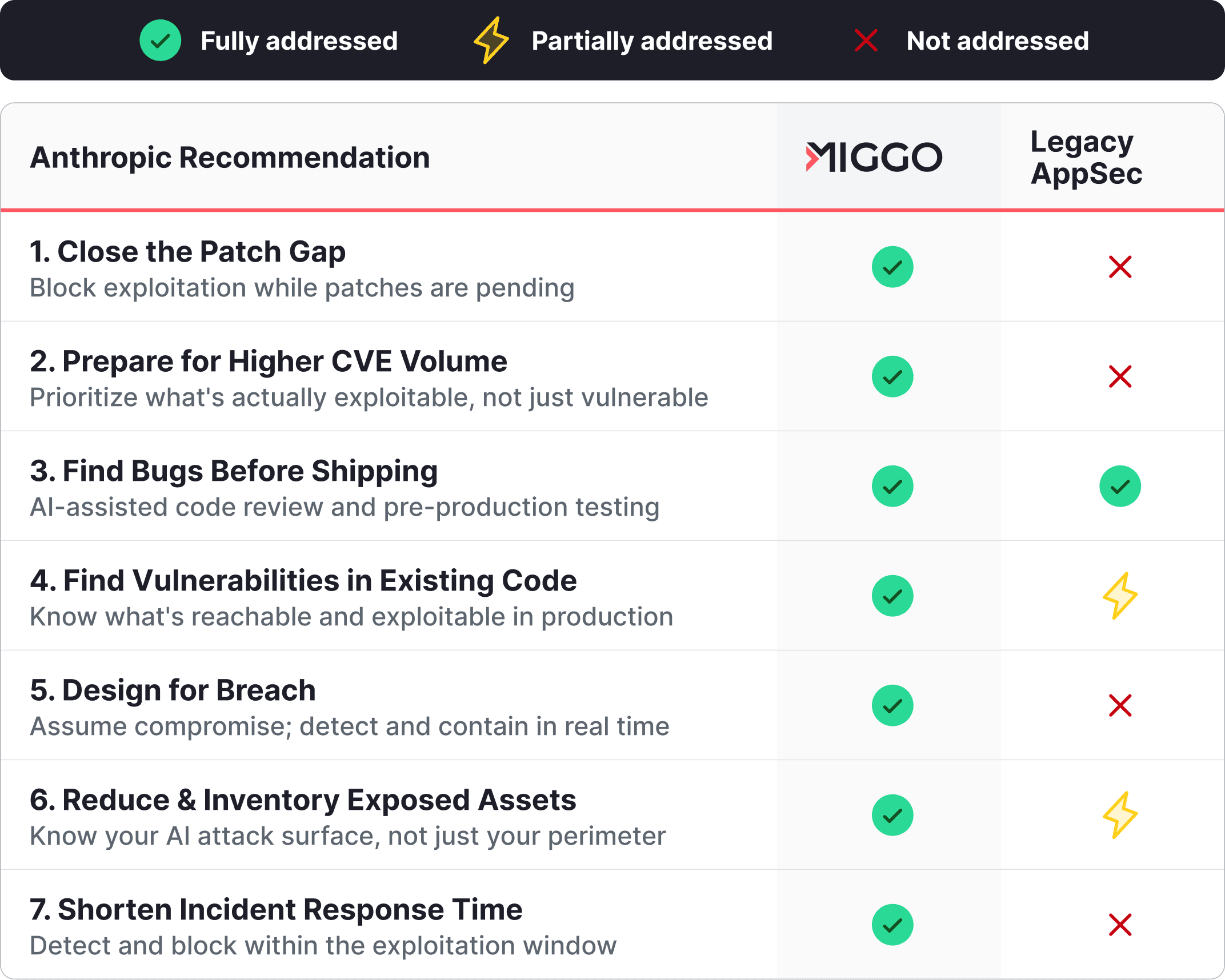
1. Close the Patch Gap
"The window between a patch being published and an exploit becoming available is shrinking."
While legacy scanners tell you what's vulnerable, they offer nothing between disclosure and deployment. This is the core problem Miggo was built to solve. Our approach — Block Now, Patch Later — isn't a workaround. It's a security architecture built for the reality that remediation will always lag discovery. Miggo operates at runtime, developing and deploying surgical WAF rules to mitigate exploitable vulnerabilities.
2. Prepare for Higher Volume Vulnerability Reports
"Look into open source software and third-party services that evaluate the reachability of vulnerable code."
AI-assisted scanning will flood teams with findings, while AI-generated code introduces more vulnerabilities. Most won't matter for your specific environment, but scanners and legacy tools will keep surfacing them, creating noise for security and developer teams. Other runtime players can tell you whether a function is reachable in code. Miggo goes further, showing which vulnerable components are reachable from the internet, tracing the full path from exposed endpoint to exploitable function in production. That's the difference between theoretical reachability and proven risk
3. Find Bugs Before Shipping Them
"Security testing needs to happen well before bugs reach production."
Pre-production testing such as SAST, DAST, and AI-assisted code review like Claude Code Security remain essential for security teams. Where Miggo contributes is context: our runtime behavioral model tells you which code paths are actually executed and how, making pre-production testing more targeted and prioritization sharper.
4. Find Vulnerabilities Already in Your Code
"Most long-running production code has never been examined by a frontier model."
Scanning code for known CVEs tells you what's theoretically vulnerable. Miggo proves real risk by combining function-level reachability with internet-level exposure, not just whether a vulnerable path exists in code, but whether real traffic is flowing through it from the outside. That inventory becomes the basis for continuous threat modeling, not a point-in-time audit. Static analysis gives you the list. Miggo tells you what's on fire and where the smoke is coming from.
5. Design for Breach
"Mitigations whose value comes from friction are much less effective against an adversary with unlimited patience."
Perimeter defense assumes attackers stop at the gate. Miggo assumes they're already inside. Our runtime detection layer baselines normal application behavior and flags deviations the moment exploitation begins. When an attacker chains calls, abuses logic, or rides ambient access, Miggo sees the behavior, not just the signature. Miggo alerts, maps the blast radius, and contains the threat before damage propagates.
6. Reduce and Inventory Exposed Assets
"You cannot defend systems you don't know about."
For AI-native applications, the attack surface includes every model, agent, tool, and MCP connection, not just IP addresses and open ports. Traditional asset inventories don't see the agentic layer. Miggo's AI runtime observability gives security teams a continuous inventory of AI components in production: what's running, what it's connected to, and what it can access.
7. Shorten Incident Response Time
"Exploits can appear within hours of a patch. Response processes that take days are too slow."
Legacy IR workflows — alert, triage, escalate, remediate — were built for human-speed attacks. Miggo's approach automates defense to stop AI-generated offense. First, instant WAF rule mitigation to close exploit attempts while teams are patching. Second, Application and Agentic Detection and Response that operates in real time, detecting exploitation attempts and blocking attacks with our patent-pending eBPF sensor.
The thread running through all seven recommendations is the same:
AI-generated offense has outpaced the tools built to stop it. Patching speed can't keep up. Signatures miss behavioral attacks. Asset inventories don't see the agentic layer. Legacy IR was built for a slower world.
Anthropic's guide describes a security architecture that proves real risk, operates at runtime, automates defense, and sees behavior, not just vulnerabilities. That's AI-automated defense to meet the moment. That's what Miggo was built to do.