TL;DR
Miggo Pulse delivers real-time vulnerability intelligence, runtime exploitability proof, and instant protection in a single workflow, purpose-built for the Mythos era
We are happy to announce the launch of Miggo Pulse, the industry's first end-to-end solution for combating AI-accelerated exploitation. Miggo Pulse is a real-time vulnerability intelligence feed that tracks emerging disclosed and undisclosed threats. It proves whether they're exploitable in your running applications and generates instant protection, all in a single workflow designed to close the patch gap before attackers can exploit it.
Designed for the Mythos moment
AI has fundamentally changed the economics of exploitation. Discovery that took skilled researchers weeks now takes hours. Working exploit logic can be generated automatically and at scale. Amid the release of frontier AI models like Mythos, security leaders across Fortune 500 organizations report receiving "stop everything" directives from their boards, demanding to know whether their applications are protected against AI-accelerated attacks.
Most security incidents don't happen because teams ignore vulnerabilities. They happen during the patch gap, the window between disclosure and deployment when attackers move in hours but patching takes weeks. The cascading effects of this acceleration are already visible: NIST has stopped enriching most CVEs after a 263% surge in submissions, HackerOne paused its Internet Bug Bounty program, and CISA's KEV catalog covers just 12% of vulnerabilities actually exploited in the wild.
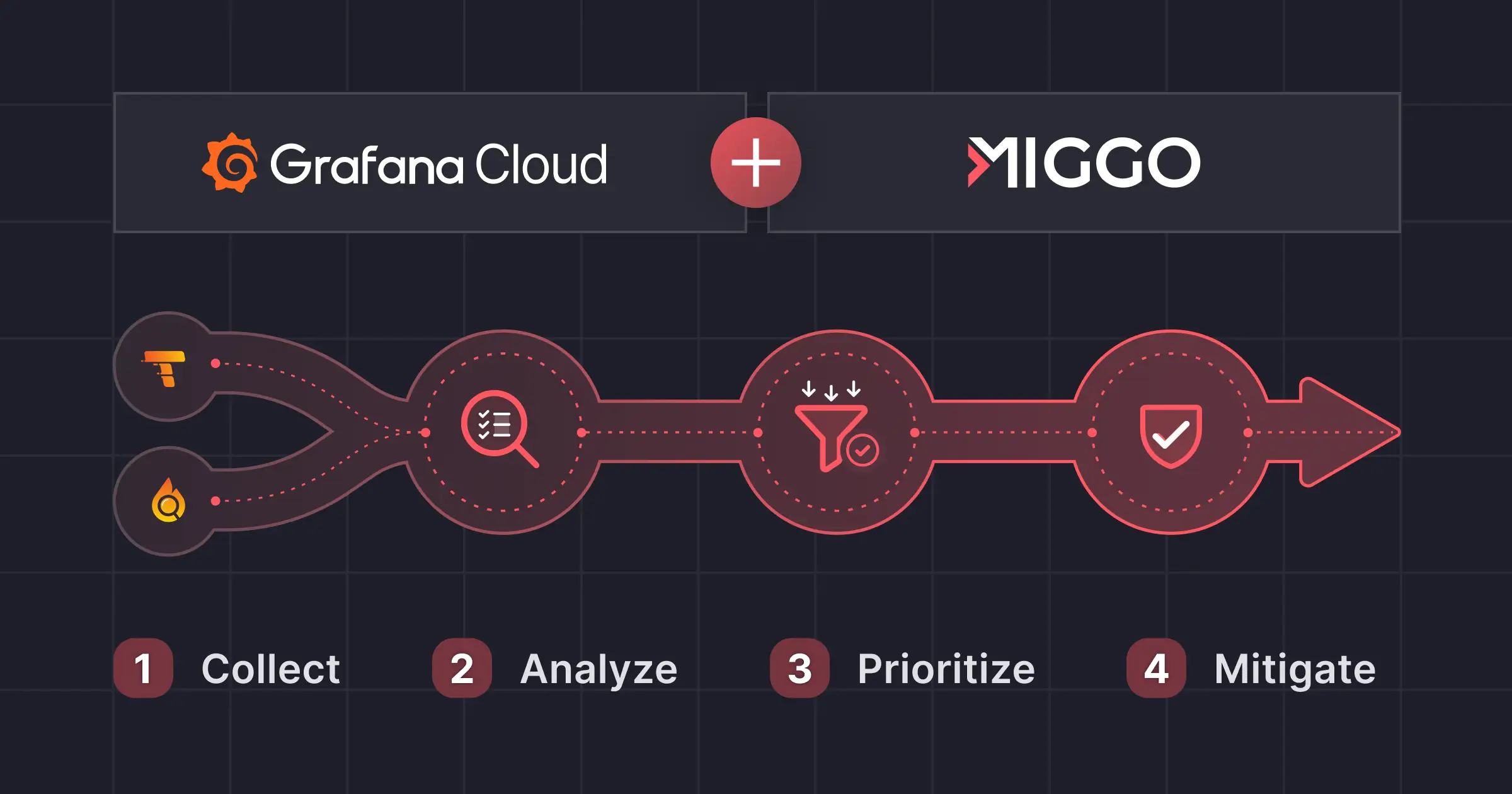
Until now, no single product has connected threat intelligence, exploitability proof, and instant protection into one workflow. Security teams have been forced to stitch together vulnerability feeds, manual triage, environment correlation, and separate mitigation tools, losing critical hours at every handoff. Miggo Pulse eliminates those gaps.
"The gap between vulnerability disclosure and exploit weaponization has collapsed. The only question left is whether your defense moves faster than their offense,"
said Daniel Shechter, CEO and Co-Founder of Miggo Security.
"Miggo Pulse is the first product that takes security teams from 'a new threat exists' to 'we're protected' in a single workflow, in minutes, not weeks."
What Miggo Pulse Does
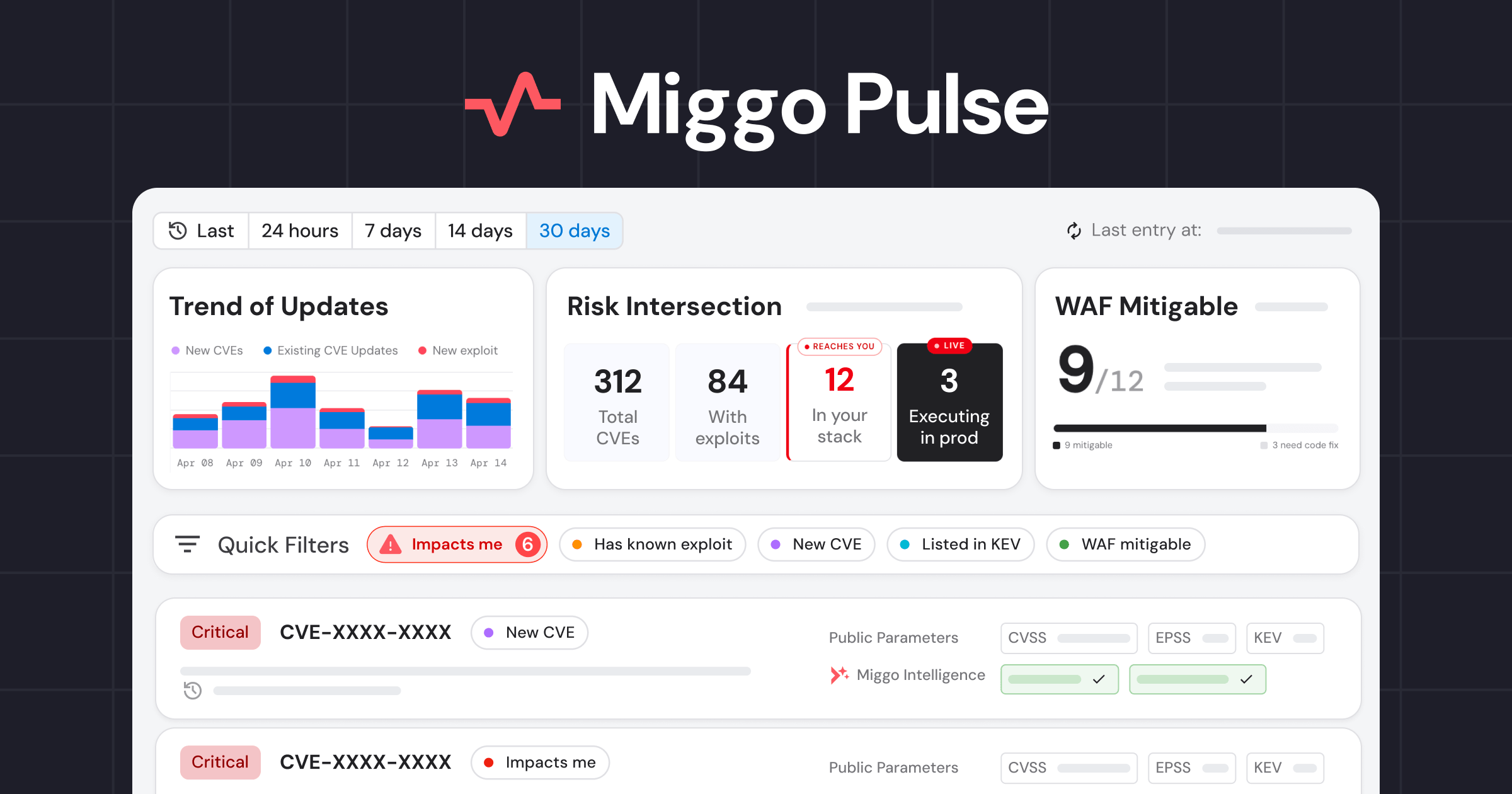
Real-time vulnerability intelligence feed. Pulse continuously tracks new CVEs, exploit releases, KEV updates, and active exploitation signals across the application ecosystem. Every vulnerability is enriched with Miggo's proprietary research: root cause analysis, vulnerable function mapping, exploit intelligence, predicted attack mutations, and identification of emerging threats before they're broadly known. This intelligence comes from Miggo's Predictive Vulnerability Database (PVD), a curated repository built by the same AI research pipeline that recently discovered critical RCE vulnerabilities in Grafana and LangChain.
Runtime exploitability proof. With Miggo's DeepTracing™ sensors deployed, Pulse automatically validates every vulnerability against your actual production environment. For each threat, you get definitive answers: is the vulnerable component running, is the code path reachable from the internet, which specific services are affected by cluster, namespace, and deployment. No manual correlation. No spreadsheets mapping CVEs to SBOMs. Proof, not guesswork.
Instant protection through WAF Copilot. When a vulnerability is confirmed as exploitable in your environment, Miggo WAF Copilot generates a customized, production-ready WAF rule tailored to the specific vulnerability and your specific environment. One click to deploy. For threats inside the perimeter, Miggo's ExploitationGuard provides runtime detection and blocking through its eBPF sensor. Two layers of defense, protecting applications while patches are developed on engineering's timeline. Before there's a patch, there's already a rule.
How Security Teams Use Miggo Pulse
- Respond to actively exploited threats: filter for new Critical/High CVEs with known exploits, get Miggo's deep analysis, and understand exposure instantly.
- Preempt evolving threats: generate customized WAF rules directly from the Pulse feed for newly published vulnerabilities before exploitation begins.
- Prioritize real risk: with sensors deployed, filter for high-severity CVEs that actually impact your running applications and focus remediation where it matters.
- Close the patch gap: deploy virtual patches in minutes for vulnerabilities where patching takes weeks or a patch doesn't exist yet.
The End-to-End Difference
Every other approach to this problem requires security teams to move between disconnected tools: one for intelligence, another for environment correlation, another for prioritization, another for mitigation. Each handoff costs time. In the Mythos era, that time is the exploit window.
Miggo Pulse is the first product that connects the full chain: intelligence arrives, exploitability is proven against your environment, and protection is generated and deployable, all from the same feed. The workflow that used to take days of triage now takes minutes.
Key Capabilities
- Real-time vulnerability intelligence with proprietary enrichment from Miggo's AI research pipeline
- Runtime validation of true exploitability through function-level reachability and internet exposure analysis
- Automatic virtual patch generation through WAF Copilot, delivering customized rules in minutes
- Dual-layer protection: WAF rules at the perimeter and eBPF-based runtime blocking
- Smart filtering by severity, exploit status, KEV listing, environment impact, and mitigation availability
- Time-based views (24h, 7d, 14d, 30d) for staying current or catching up
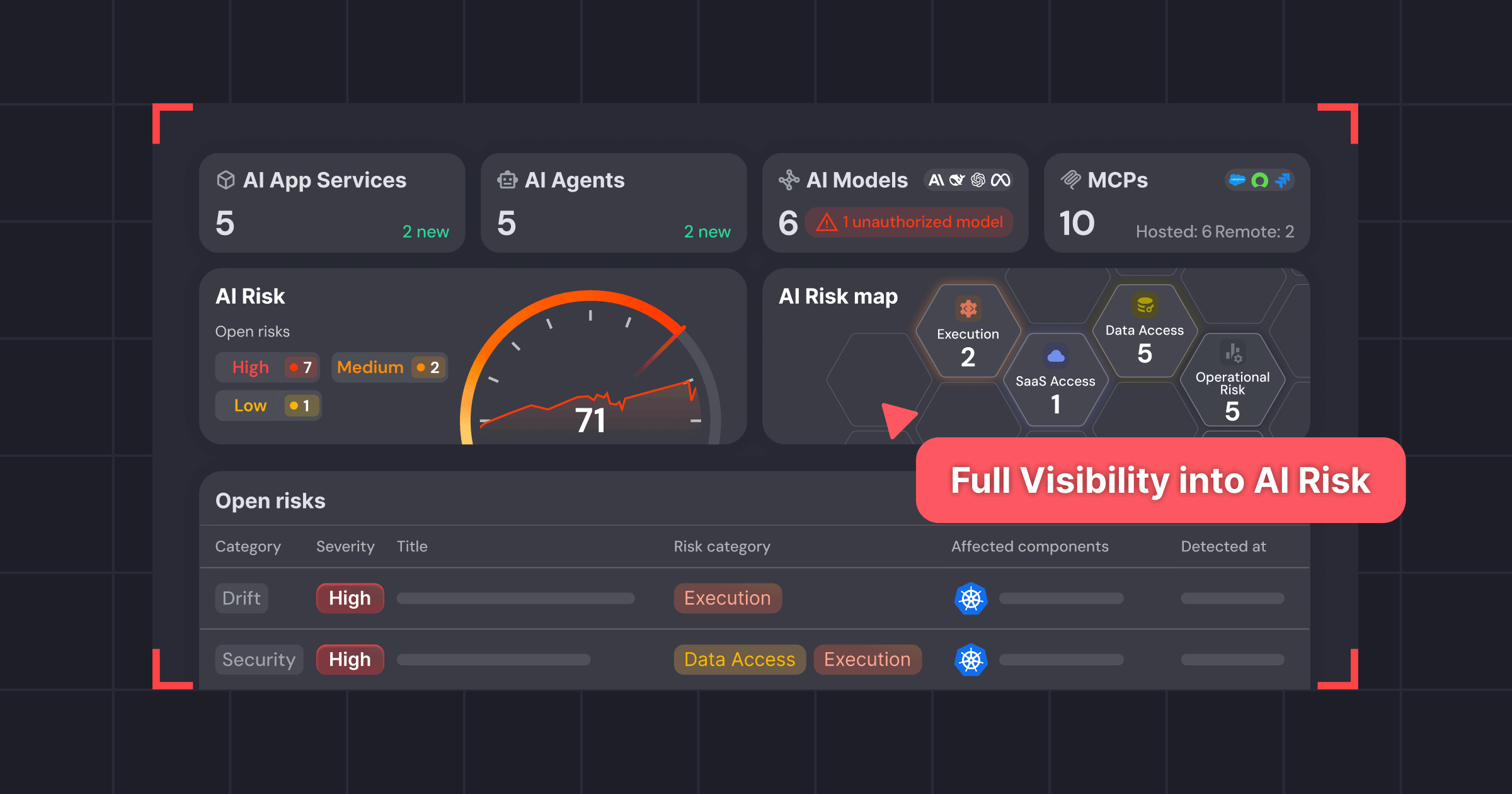
- AppDNA runtime mapping for continuous application inventory
- API and MCP access for integration into existing security workflows
Learn more in the walkthrough.